Zero-Day Detection: Identifying Signatureless Threats in 2026

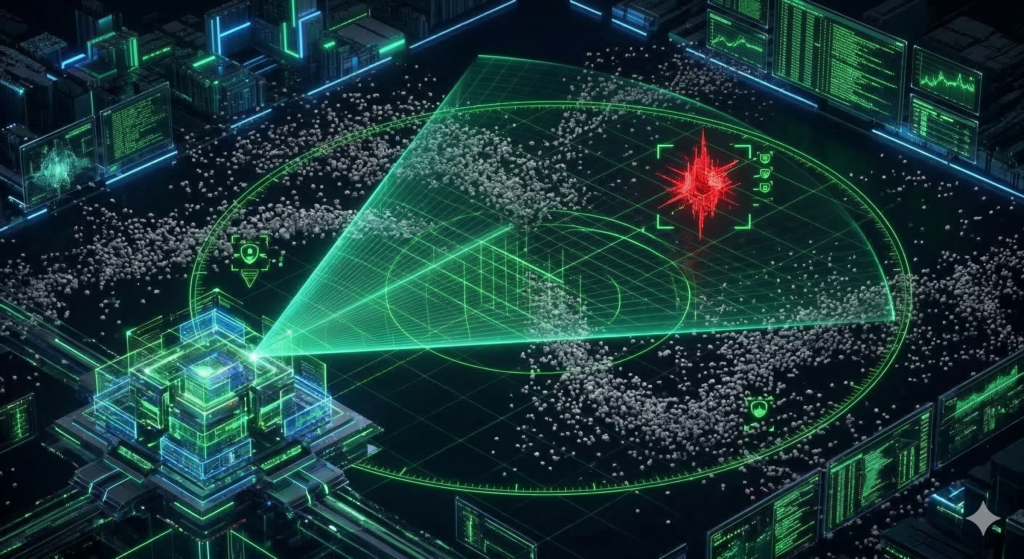
In today’s dynamic cybersecurity ecosystem, relying solely on signature databases is an obsolete and dangerous strategy. “Zero-Day” attacks exploit vulnerabilities unknown to manufacturers, meaning no “patch” or antivirus signature exists to stop them at the moment of initial impact. For organizations, this represents the greatest challenge in operational visibility.
Modern defense requires a transition toward anomaly-based detection and behavioral analysis. It is not about knowing exactly what the threat is, but identifying that its behavior is not normal within your infrastructure.
The Problem in Brief: The Invisibility of the Unknown Attack
The primary risk of a Zero-Day is its ability to evade traditional security controls for days or even weeks. A critical industry datum reveals that human error and weak configurations often facilitate the lateral movement of these threats once they have bypassed the perimeter.
Without a proactive monitoring strategy, organizations suffer from “alert fatigue” in the face of thousands of irrelevant events, while the true silent intrusion goes unnoticed. The direct consequence is massive data loss and total network compromise before a global alert is ever issued.
The Solution: Defensive Intelligence and Advanced Monitoring
To neutralize threats that no one has seen before, it is imperative to implement a defense model that constantly learns and evolves.
Expert Vigilance and Threat Hunting
Implementing a SOC that operates 24/7 is fundamental to detecting the invisible. Through “Threat Hunting,” our analysts actively search for indicators of compromise that do not depend on signatures, but on suspicious execution patterns within the network.
Log Management and Behavioral Analysis
To identify a Zero-Day, it is necessary to correlate data from multiple sources. Utilizing robust log analysis allows for processing large volumes of data to find the needle in the haystack. By analyzing traffic in real-time, we can block connections to command-and-control servers before the attack is completed.
Hardening Critical Assets
The best defense against the unknown is reducing the attack surface through the Hardening of servers and workstations. By closing unnecessary ports and restricting privileges, we limit a Zero-Day’s ability to propagate, gaining valuable time for Digital Forensics specialists to analyze the sample and generate a response.
Conclusion
Zero-Day attack detection is the ultimate test of your defense team’s maturity. It requires a strategic alliance between cutting-edge technology and the judgment of expert analysts who “sleep with one eye open”. At Hacking Mode, we transform the uncertainty of the unknown into a resilient response capability that ensures your business continuity.
👉 STRENGTHEN YOUR DEFENSE WITH HACKING BLUE
🌎 GLOBAL ATTENTION & COVERAGE
📞 Phone / WhatsApp:
- 🇲🇽 MX: +52 1 55 5550 5537
- 🇺🇸 USA: +1 (918) 540-9341
📧 Email Support & Sales:
🌐 Global Coverage & Service Locations
We provide immediate attention, strategic consulting, and deployment of Security Compliance Specialists and Cybersecurity Experts across the entire Americas, ensuring business continuity in the main markets of:
- 🇺🇸 United States: Miami, Houston, New York, San Francisco, Los Angeles, among others.
- 🇲🇽 Mexico: Mexico City (CDMX), Monterrey, Guadalajara, Queretaro, Tijuana (Nationwide Coverage).
- 🇬🇹 Guatemala: Guatemala City, Quetzaltenango, Escuintla, Antigua Guatemala (Nationwide Coverage).
- 🌎 Latin America: Bogota, Medellin, Lima, Santiago de Chile, Buenos Aires, Sao Paulo, Panama City, serving the entire region.
Tags:
#HackingMode #Cybersecurity #ZeroDayDetection #HackingBLUE #SignaturelessDefense